random gallery image
random tutorial
 preview
preview..one or more modules you must have seen the iframes used for realtime result display. In this tutorial I'm going to show you how to insert them into your module and how they..
random vulnerability assesment

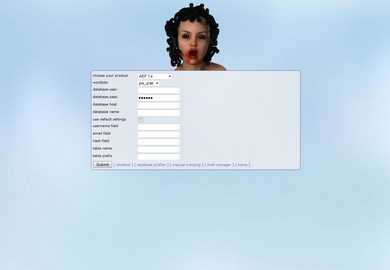
Mister LG
Mister LG can create upload forms and test targets on file upload vulnerabilities
HackSuite File Library
File Library
 Here you can find the latest files and structure of the THC HackSuite, note that if you have an earlier version of the suite it's not recommended to update files manually. Instead you should overwrite your existing HackSuite environment.
Here you can find the latest files and structure of the THC HackSuite, note that if you have an earlier version of the suite it's not recommended to update files manually. Instead you should overwrite your existing HackSuite environment.
<?php
/*
Very basic single user login test system, no paths defined we want to keep it very fast
Author: Remco Kouw
Site: http://www.hacksuite.com
Last Edit: 25-02-2015
*/
define('IN_SCRIPT',1);
// set some paths
$_ROOT = str_replace("/TestServers","",substr($_SERVER['SCRIPT_FILENAME'],0,strrpos($_SERVER['SCRIPT_FILENAME'],"/")));
$sCurrentFile = substr($_SERVER['SCRIPT_FILENAME'],strrpos($_SERVER['SCRIPT_FILENAME'],"/")+1);
// get the current log folder
$_DYNAMIC_ROOT = "..";
include_once("../vars.php");
include_once("../paths.php");
$aLogFolder = explode("/",$_PATHS['log_root']);
$sLogFile = $_ROOT."/".$aLogFolder[(count($aLogFolder)-1)]."/".$sCurrentFile;
// include setup based upon file path
include_once($_ROOT."/Includes/server_setup.php");
// check if we have logging enabled first, if so let's see if the ip address has been banned
if($_CONFIG['iUseLog']==1){
$iAttempts = 0;
$aFile = @file($sLogFile);
for($x=0;$x<count($aFile);$x++){
if(count($aData = @explode("|",$aFile[$x]))==2){
// calculate the amount of failures for the client
if($aData[0]>=(time()-intval($_CONFIG['iBanTimeSpan'])) && $_SERVER['REMOTE_ADDR']==trim($aData[1])){
$iAttempts++;
}
}
}
if($_CONFIG['iAttempts']<=$iAttempts){
echo $_CONFIG['sBanned'];
exit;
}
// not banned..let's proceed
}
// did we sent the form in order to login?
if(isset($_POST['user'])){
if($_POST['user']==$_CONFIG['sUser'] && $_POST['pass']==$_CONFIG['sPass']){
// return success message
echo $_CONFIG['sHacked'];
// if logging is enabled clean it
if($_CONFIG['iUseLog']==1 && filesize($sLogFile)!=0){
WriteF($sLogFile,"","w");
}
}
else{
// failed, if logging is enabled, log this attempt
if($_CONFIG['iUseLog']==1){
include_once($_ROOT."/Functions/fwrite.php");
// ip ban if user exceeded max login attempts
if($iAttempts!=0 && $iAttempts>=$_CONFIG['iAttempts']){
echo $_CONFIG['sBanned'];
exit;
}
// log the failure
if(!WriteF($sLogFile,time()."|".$_SERVER['REMOTE_ADDR']."\n","a")){
echo"<p>Failed to write to log file <b>$sLogFile</b>";
exit;
}
}
$iSleep = intval($_CONFIG['iSleep']);
if(is_int($iSleep)){
// will result in a timeout, if the value is too high
sleep($_CONFIG['iSleep']);
}
echo $_CONFIG['sFailed'];
}
}
else{
// create login form
echo"<html>\n";
echo"<head>\n";
echo"<title>Very Basic Login System</title>\n";
echo"<meta http-equiv=\"Content-Type\" content=\"text/html; charset=iso-8859-1\">\n";
echo"<style type=\"text/css\">\n";
echo"<!--\n";
echo"body { font-family:Arial,Verdana,Helvetica;font-size:10px;color:#c0c0c0; }\n";
echo"-->\n";
echo"</style>\n";
echo"</head>\n";
echo"<body>\n";
echo"<form method=\"post\">\n";
echo"<b>username:</b> <input type=\"text\" name=\"user\"><br>\n";
echo"<b>password:</b> <input type=\"password\" name=\"pass\"><br>\n";
echo"<input type=\"submit\" name=\"submit\" value=\"Login\">\n";
echo"</form>\n";
echo"</body>\n";
echo"</html>";
}
?>
powered by
site stats
cms statistics:
version: 0.6.0downloads: 4384
native: 26
modules: 21
apps: 2
support development
It takes lots of calories in order to create new things for the hacksuite, so it would be grand if you could buy me a protein shake or extra energy to keep me going. Thanks!
disclaimer
We are not responsible for any direct or indirect damage caused by abusing the tools provided on hacksuite.com. The suite is developed for educational purposes, use at your own risk!
site resources
remote resources
partners and friends